Tag: Security Research
-
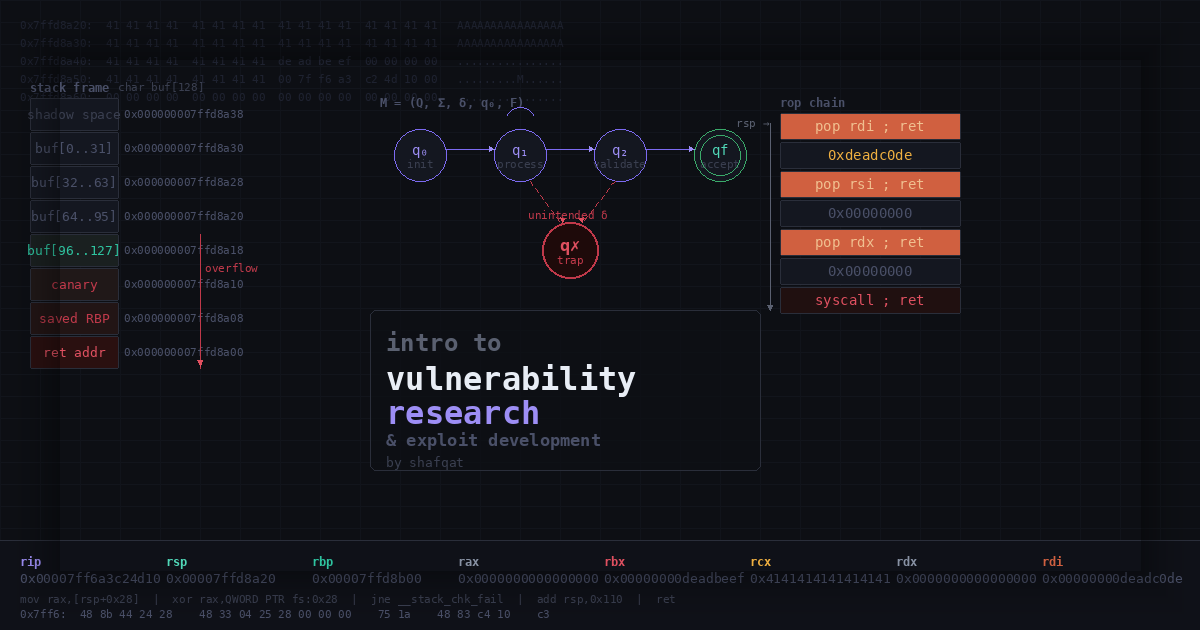
Introduction to Vulnerabilities
by shafqat stack buffer overflows i want to preface this by saying this took me a while to actually understand. not because the concepts are impossibly hard, but because most of the material out there is either too surface-level (“send a long string and overwrite EIP!”) or assumes you already know what you’re doing. there…